Privacy preserving multi-party computation delegation for deep learning in cloud computing - ScienceDirect

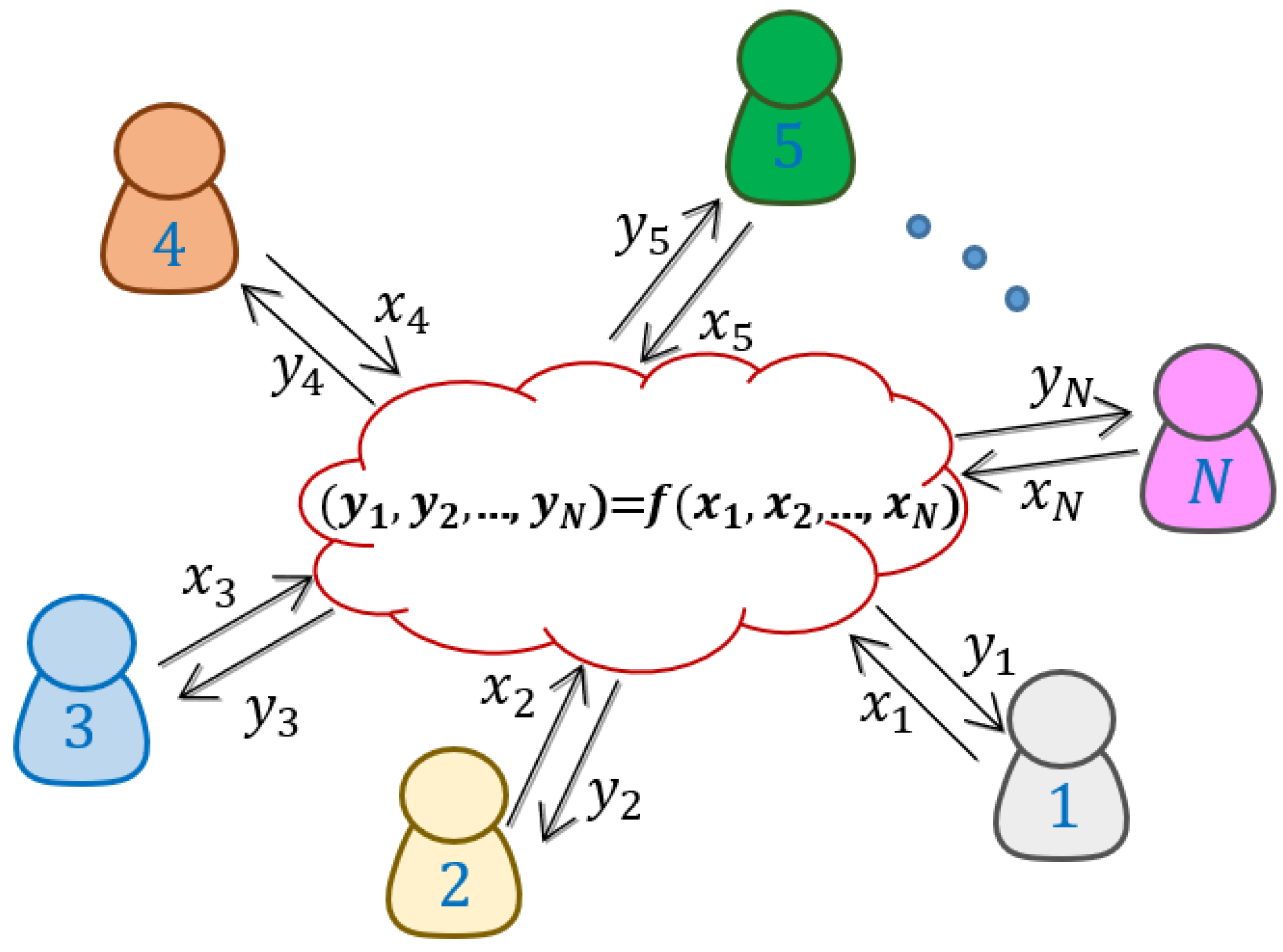
Privacy-Preserving Global Model Construction through Secure Multiparty... | Download Scientific Diagram

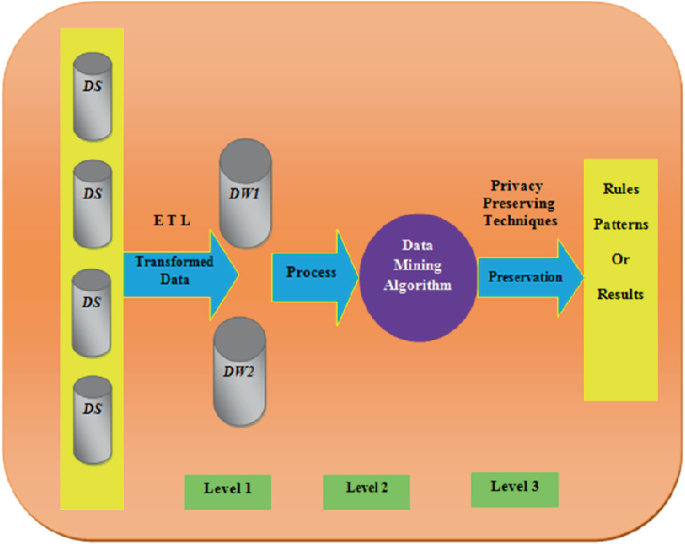
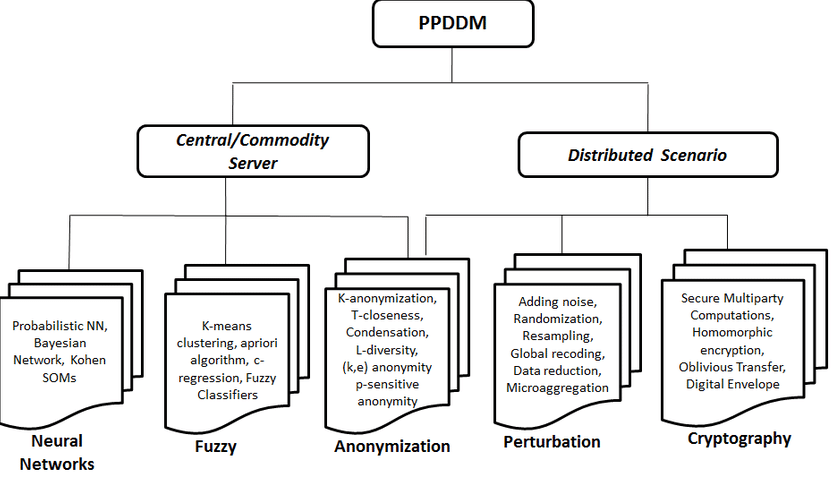
A Review Study on the Privacy Preserving Data Mining Techniques and Approaches | Manish Sharma and Manish Mathuria - Academia.edu
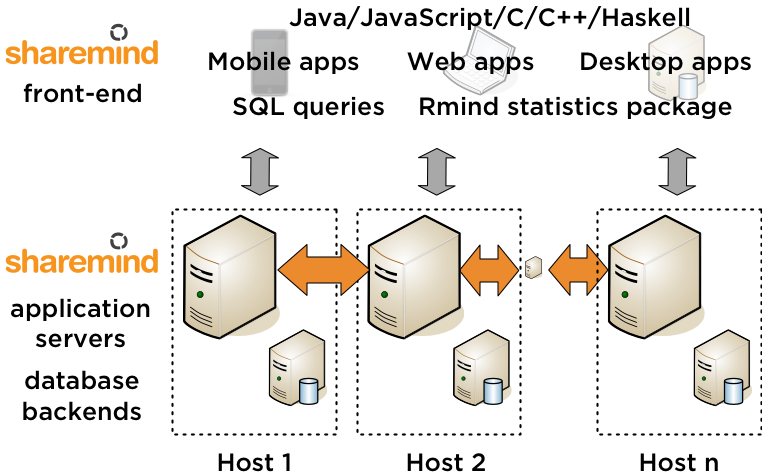
Privacy Preserving Medical Data Analytics using Secure Multi Party Computation. An End-To-End Use Case.
![PDF] Secure Multiparty Computation during Privacy Preserving Data Mining: Inscrutability Aided Protocol for Indian Healthcare Sector | Semantic Scholar PDF] Secure Multiparty Computation during Privacy Preserving Data Mining: Inscrutability Aided Protocol for Indian Healthcare Sector | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/54858338e517a3112133e7e664d762299842671b/5-Figure2-1.png)
PDF] Secure Multiparty Computation during Privacy Preserving Data Mining: Inscrutability Aided Protocol for Indian Healthcare Sector | Semantic Scholar

Analysis and Evaluation of Schemes for Secure Sum in Collaborative Frequent Itemset Mining across Horizontally Partitioned Data
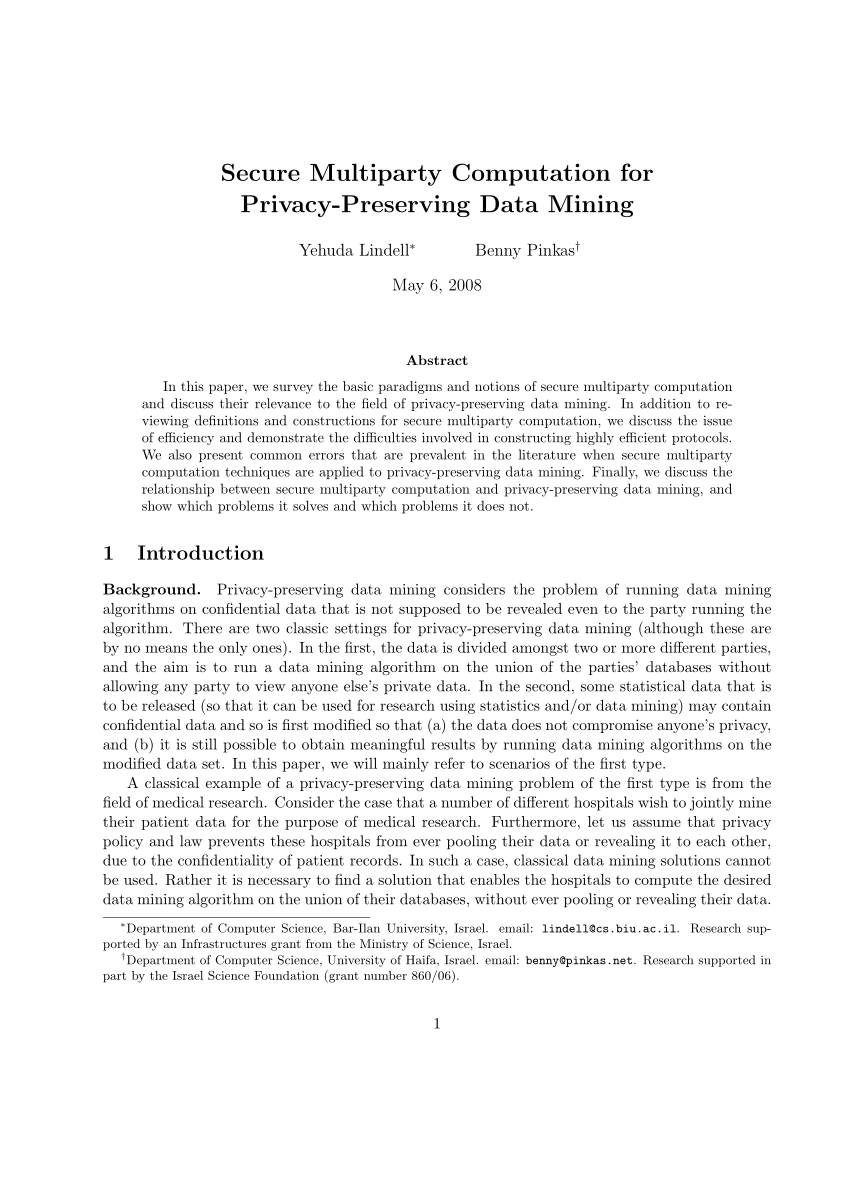
Week 5 Reading Assignment: “Secure Multiparty Computation for Privacy-Preserving Data Mining“ Discussion Summary Question
Applied Sciences | Free Full-Text | Generation and Distribution of Quantum Oblivious Keys for Secure Multiparty Computation
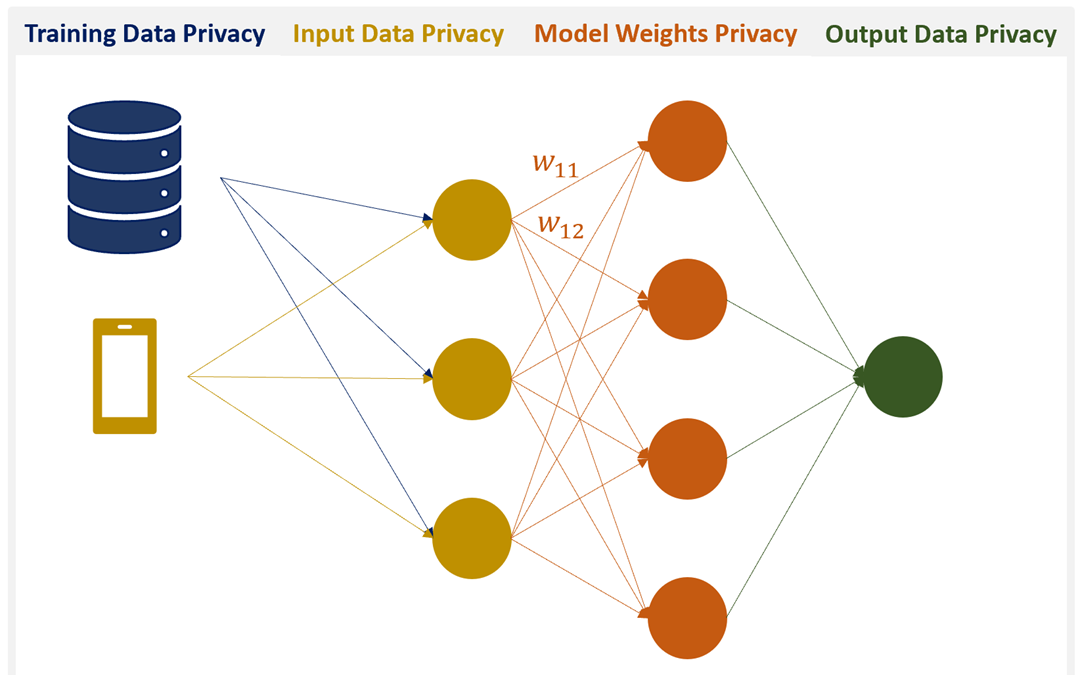
Perfectly Privacy-Preserving AI. What is it and how do we achieve it? | by Patricia Thaine | Towards Data Science

PDF) Fostering the Uptake of Secure Multiparty Computation in E-Commerce | Octavian Catrina and Octavian Catrina - Academia.edu
![PDF] Secure Multiparty Computation during Privacy Preserving Data Mining: Inscrutability Aided Protocol for Indian Healthcare Sector | Semantic Scholar PDF] Secure Multiparty Computation during Privacy Preserving Data Mining: Inscrutability Aided Protocol for Indian Healthcare Sector | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/54858338e517a3112133e7e664d762299842671b/8-Figure4-1.png)
![PDF] Secure Multiparty Computation for Privacy-Preserving Data Mining | Semantic Scholar PDF] Secure Multiparty Computation for Privacy-Preserving Data Mining | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/55682d5db7f02b99ee979c3cda256b5db494c6fb/2-Figure1-1.png)