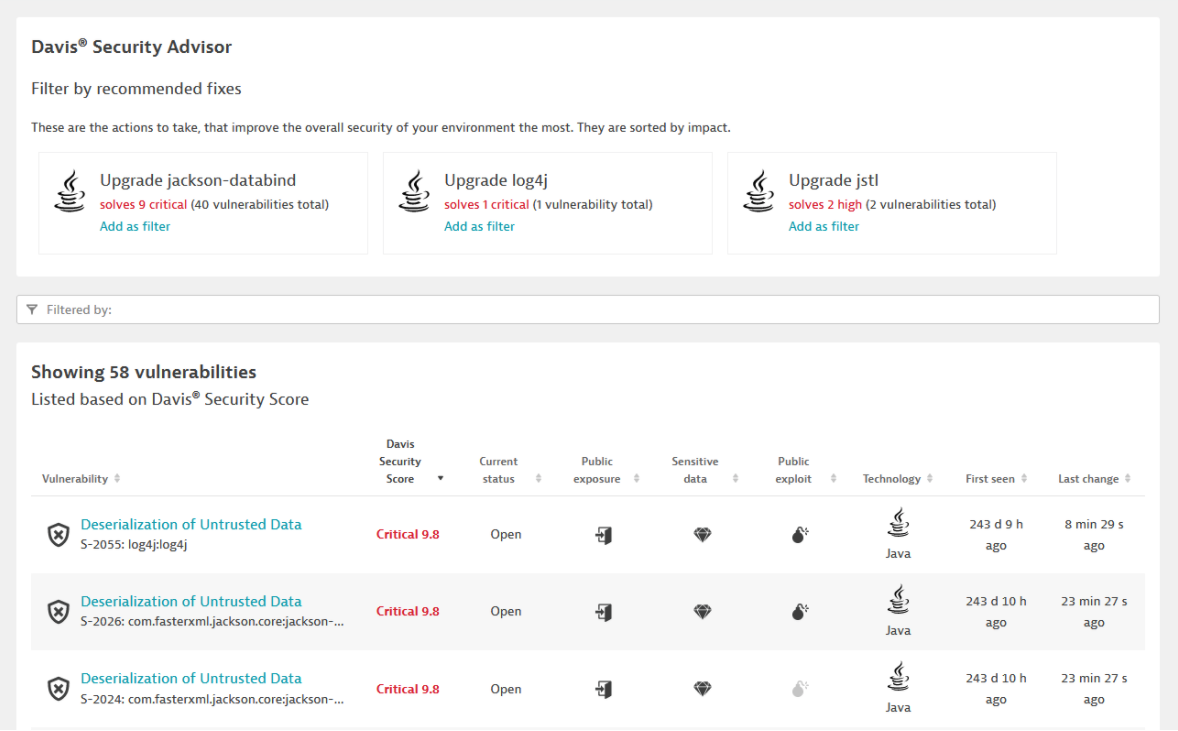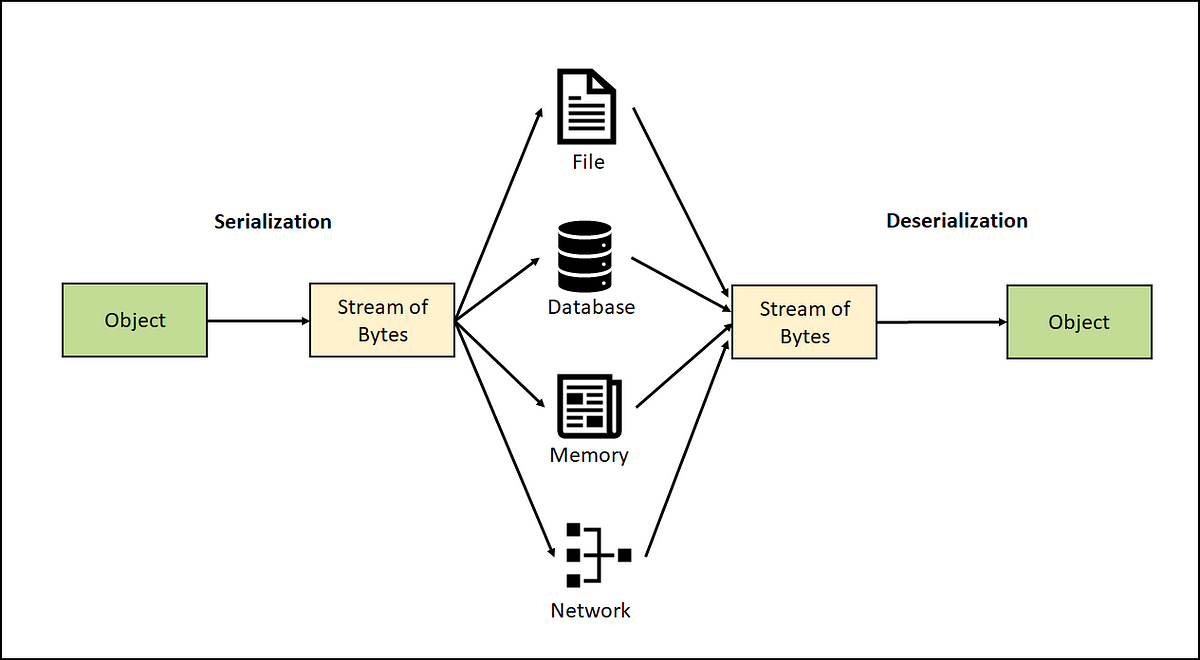
Serialization Filtering — Deserialization Vulnerability Protection in Java | by Albin Issac | Tech Learnings | Medium
GitHub - EdoardoVignati/java-deserialization-of-untrusted-data-poc: Some PoC (Proof-of-Concept) about vulnerability of java deserialization of untrusted data
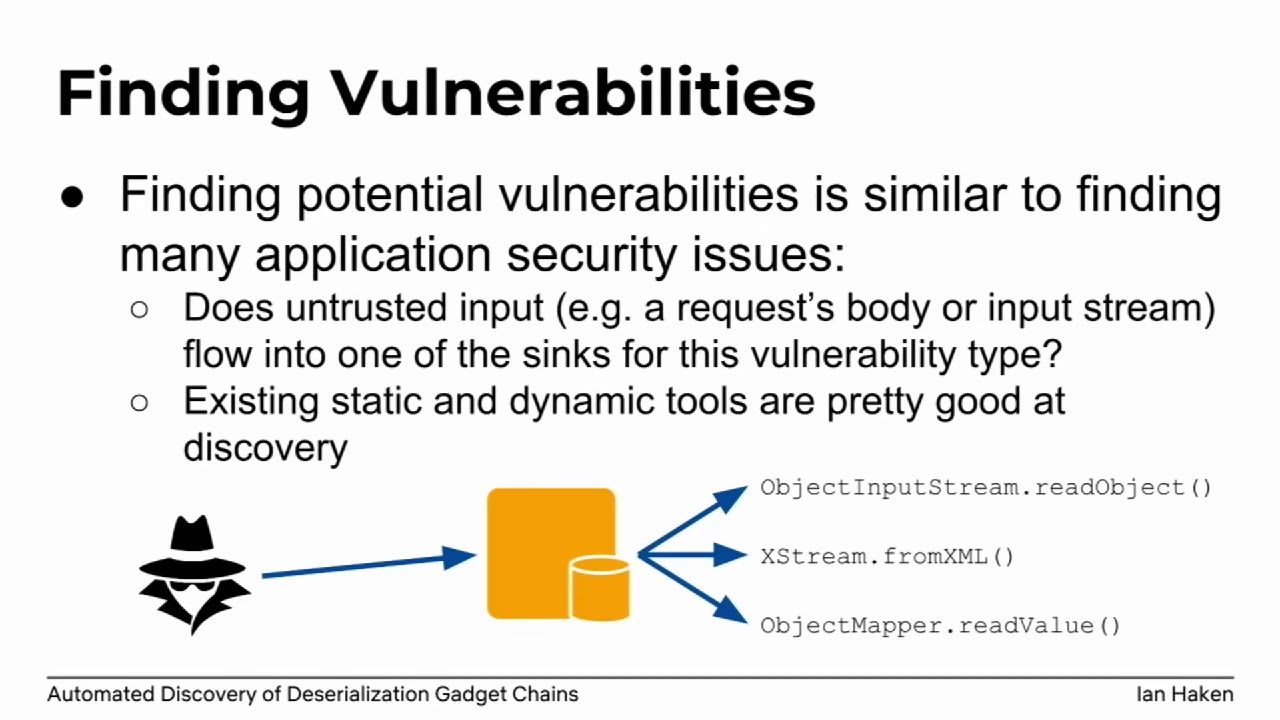
Dealing with Deserialization of Untrusted Data in Java Applications - GBHackers - Latest Cyber Security News | Hacker News

Checkmarx Research: Apache Dubbo 2.7.3 – Unauthenticated RCE via Deserialization of Untrusted Data (CVE-2019-17564) | Checkmarx.com

SSD Advisory – Microsoft SharePoint Server WizardConnectToDataStep4 Deserialization Of Untrusted Data RCE - SSD Secure Disclosure